
Nightowl
-
Posts
1,858 -
Joined
-
Days Won
17
Posts posted by Nightowl
-
-
I will give it a try , thank you.
Can I upgrade with my current license or I need a different kind of license?
-
23 minutes ago, Dave12345 said:
KB5025221 is already installed on the system since the 12/04. So I'm unsure what ESET is reporting is uninstalled/not updated. If it is indeed KB4023057, where it's pulling that back from is something of a mystery.
Again, thanks for your replies. Much appreciated.
It's weird then , let's wait for a reply from ESET staff , they know more than me.
And you are welcome bro.
-
5 minutes ago, Dave12345 said:
Here is the result from Powershell:
Title : INTEL - System - 7/18/1968 12:00:00 AM - 10.1.11.2 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : INTEL System driver update released in July 1968 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 12/07/2018 12:00:00 AM MaxDownloadSize : 25394 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : OtherHardware DriverHardwareID : pci\ven_8086&dev_a2b1 DriverManufacturer : INTEL DriverModel : Intel(R) Thermal subsystem - A2B1 DriverProvider : INTEL DriverVerDate : 18/07/1968 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25174016 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : INTEL - System - 7/18/1968 12:00:00 AM - 10.1.11.2 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : INTEL System driver update released in July 1968 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 12/07/2018 12:00:00 AM MaxDownloadSize : 25394 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : OtherHardware DriverHardwareID : pci\ven_8086&dev_a294 DriverManufacturer : INTEL DriverModel : Intel(R) PCI Express Root Port #21 - A2EB DriverProvider : INTEL DriverVerDate : 18/07/1968 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25174026 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : LG - Monitor, Other hardware - LG ULTRAWIDE(HDMI) AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : LG Monitor, Other hardware software update released in August, 2015 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 06/09/2018 12:00:00 AM MaxDownloadSize : 25674 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : OtherHardware DriverHardwareID : monitor\gsm59f1 DriverManufacturer : LG DriverModel : LG ULTRAWIDE(HDMI) DriverProvider : LG DriverVerDate : 26/08/2015 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25190410 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : Realtek Semiconductor Corp. - MEDIA - 8/22/2017 12:00:00 AM - 6.0.1.8237 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : Realtek Semiconductor Corp. MEDIA driver update released in August 2017 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 11/09/2018 12:00:00 AM MaxDownloadSize : 135892414 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : Sound DriverHardwareID : hdaudio\func_01&ven_10ec&dev_0867&subsys_103c8473 DriverManufacturer : Realtek DriverModel : Realtek High Definition Audio DriverProvider : Realtek Semiconductor Corp. DriverVerDate : 22/08/2017 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25174026 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : INTEL - System - 7/18/1968 12:00:00 AM - 10.1.14.4 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : INTEL System driver update released in July 1968 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 12/07/2018 12:00:00 AM MaxDownloadSize : 23744 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : System.__ComObject UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : OtherHardware DriverHardwareID : pci\ven_8086&dev_3ec2 DriverManufacturer : INTEL DriverModel : Intel(R) Host Bridge/DRAM Registers - 3EC2 DriverProvider : INTEL DriverVerDate : 18/07/1968 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25165834 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : Realtek Semiconductor Corp. - USB - 4/26/2019 12:00:00 AM - 10.0.18362.31248 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : Realtek Semiconductor Corp. USB driver update released in April 2019 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 10/06/2019 12:00:00 AM MaxDownloadSize : 1756364 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : System.__ComObject UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : OtherHardware DriverHardwareID : usb\vid_0bda&pid_0153 DriverManufacturer : Realtek Semiconductor Corp. DriverModel : Realtek USB 2.0 Card Reader DriverProvider : Realtek Semiconductor Corp. DriverVerDate : 26/04/2019 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25174026 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2 Title : HP Inc. - Firmware - 15.52.0.0 AutoSelectOnWebSites : False BundledUpdates : System.__ComObject CanRequireSource : False Categories : System.__ComObject Deadline : DeltaCompressedContentAvailable : False DeltaCompressedContentPreferred : True Description : HP Inc. Firmware driver update released in June 2020 EulaAccepted : True EulaText : HandlerID : hxxp://schemas.microsoft.com/msus/2002/12/UpdateHandlers/WindowsDriver Identity : System.__ComObject Image : InstallationBehavior : System.__ComObject IsBeta : False IsDownloaded : False IsHidden : False IsInstalled : False IsMandatory : False IsUninstallable : False Languages : System.__ComObject LastDeploymentChangeTime : 27/09/2020 12:00:00 AM MaxDownloadSize : 5904715 MinDownloadSize : 0 MoreInfoUrls : System.__ComObject MsrcSeverity : RecommendedCpuSpeed : 0 RecommendedHardDiskSpace : 0 RecommendedMemory : 0 ReleaseNotes : SecurityBulletinIDs : System.__ComObject SupersededUpdateIDs : System.__ComObject SupportUrl : hxxp://support.microsoft.com/select/?target=hub Type : 2 UninstallationNotes : UninstallationBehavior : System.__ComObject UninstallationSteps : System.__ComObject KBArticleIDs : System.__ComObject DeploymentAction : 4 DownloadPriority : 2 DownloadContents : System.__ComObject DriverClass : Firmware DriverHardwareID : uefi\res_{f6f61e15-84e2-4a11-91c9-1e3291e4c223} DriverManufacturer : HP Inc. DriverModel : System Firmware DriverProvider : HP Inc. DriverVerDate : 15/06/2020 12:00:00 AM DeviceProblemNumber : 0 DeviceStatus : 25174026 RebootRequired : False IsPresent : False CveIDs : System.__ComObject BrowseOnly : False WindowsDriverUpdateEntries : System.__ComObject PerUser : False AutoSelection : 1 AutoDownload : 2If I'm reading that correctly, they are all optional updates for firmware/drivers.
@Nightowl - I was unaware they shared the same KB number for different patches. That seems like such a bad policy (but that's besides the point).
In regards to 2023-04, I have a optional preview update available - KB5025297. My understanding is that KB5025297 is basically beta and MS they want users to test it? But in terms of KB4023057, that doesn't show anywhere as being available. UI or Powershell (unless I missed something above). So I don't know how ESET is reporting it?
Thank you all for your help.
Yes KB5025297 is Preview : https://support.microsoft.com/en-us/topic/april-25-2023-kb5025297-os-build-19045-2913-preview-a5e3f0ce-b9f1-40b9-a3fa-42b8093f3873
And I believe ESET is reporting for this KB5025221
You can see them here : https://www.catalog.update.microsoft.com/Search.aspx?q=cumulative+update+windows+10+x64
-
1 hour ago, Dave12345 said:
ESET Internet Security quite regularly incorrectly states that updates are available and not installed for Windows 10. See below a screenshot as of this morning:
Thanks in advance.
In the provided screenshot it's stated wrong
You applied 2023-01 , ESET is showing 2023-04
Hence the install date , January , which each month should be a new update , 01 Jan , 02 Feb , 03 March , 04 April etc.. , but the missing months you have will be included in the latest one you will download.
Microsoft releases that Cumulative Update , monthly , second Tuesday of the month , you will have the cumulative update package from MS
-
41 minutes ago, Damjan said:
Why ESET don't detected BonziBuddy Virus!
In the first comment of the video

I think the detection is through PUA detections
https://help.eset.com/glossary/en-US/unsafe_application.html?unwanted_application.html
-
1 hour ago, czesetfan said:
Is it possible to expect such a development? A GUI on basic options would be enough.
Or is it really that costly to maintain a Home Edition even for a small audience?
I don't know bro , it's just my imagination as I don't work for ESET.
-
On 4/22/2023 at 11:37 AM, curano said:
23.04
I believe it isn't supported
QuoteUbuntu 23.04 is shipped with the new 6.2 Linux kernel
22.04 have kernel 5.15 which is the latest version that is supported by endpoint linux.
https://help.eset.com/eeau/91/en-US/?system_requirements.html
-
I'd recommend jumping to ESET Cloud and protect the Linux machines from there with Endpoint Linux
It's recommended but still you need to buy the minimum amount of licenses to have a Business Account.
QuoteLinux almost 3% of the global desktop market share - Jan 2022 and Dec 2022 : r/linux.
It explains almost why you rarely find a Home edition for Linux version not only here with ESET , and we find Endpoint one because some linux machines have to be protected at work environments
It is true same goes for home linux , but it's not a priority I bet , but I imagine , once the product as GUI is fully ready in Endpoint , it will be made for Home version , since endpoint version is controlled through ESET Protect
-
On 10/18/2022 at 10:07 AM, Pumaferox said:
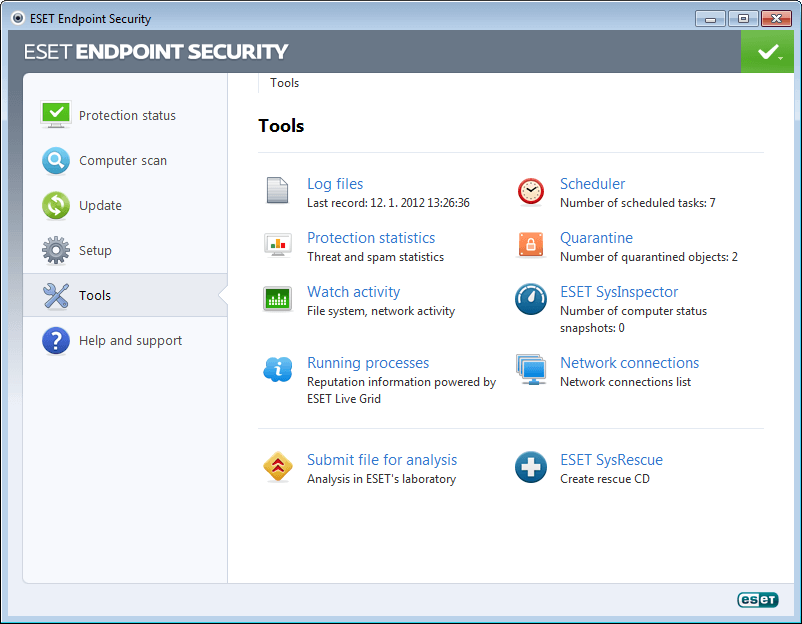
Description: Show all the tools when clicking on "Tools", not only three of them
Detail: It seems rather unnecessary that you have to click on "Tools" and then on "More Tools" since the "Tools" page only shows 3 tools, completely wasting space.Also, take a look at ESET Endpoint Security ver.5. It was way better this way; just a click on "Tools" brings you a complete overview, nice and tidy. Please bring it back this way!
I agree on this one, before clicking on Tools seeing all of the stuff together was easier on the eyes and less clicking
-----
Just another suggestion that isn't important , give us the ability to choose the old ESET icon , old school one

What difference it makes ? nothing , just nostalgia

-
2 minutes ago, Marinos said:
I don't think it blocked it. It just says connected 6 days ago. Since then it hasn't logged in again. Or tried anyway.
I understood what you mean now,
The Network Scanner that shows you which devices were inside your LAN
Incase it's your LAN and it shows some Public IP from the scan , can you post a screenshot of it ? , you can blur most of the IP if you don't want to show it.
And also for your better peace of mind , update your router to latest version offered by manufacturer , and change your WIFI passwords and check the computers that are connected in the network that they aren't somehow infected (could be not).
-
12 hours ago, Marinos said:
Couldn't be someone that logged into their wifi ?
When ESET shows blocked attempts in Firewall logs or in Network Troubleshooter
It means that the firewall is working and blocking attempts from the Internet
But for example if you are connected to an Office WIFI or Home WIFI , and yet you are still seeing some Public IP addresses are trying to communicate with your PC , then you have to check your router and properly configure the firewall to block or reject all Incoming connections and keep All Outgoing as allowed , this incase you don't use any kind of service or portforwarding inside your LAN and have no need to come from Internet Side to Office/Home side.
-
Since you modified it brother , you broke the signature, you modified the contents as then the signature of the maker is broken
 This will give an indicator to A.I scanners that this file might be malicious.
This will give an indicator to A.I scanners that this file might be malicious.
Because the A.I usually knows this software/installer as trusted and signed , then suddenly you uploaded it differently and unsigned , it will look suspicious to the Bots(A.I).
The new un-modified installer that you uploaded got 2 detections , those are false-positives , the A.I might detect them because installer is new , it might feel it's a bit suspicous
once you played with the HEX and added ZEROs, 2 more A.I hated your modification and found it suspicious and also you broke the signature of the developers.
Since I was marked as a solution , I may be wrong or not 100% accurate , if I am mistaken , please correct me
- el el amiril and itman
-
 2
2
-
7 hours ago, Gary Luk said:
Sorry , my missleading that my boxset license also support ESET Antivius for Linux. So is it support QTS OS?
I believe so not , but you can make it a bit different
Connect the drive to some endpoint and you can force the endpoint to scan there , I think that works . but very slow.
-
Since AVs mark those applications as SAFE , most of their actions would be considered to be normal to the AVs if not all of their actions , and it's why malware developers get into the hassle of using a legit software for their illegal operation.
-
Thank you also Peter for assistance
One last note is after clearing everything , one should reset Windows Firewall settings incase it's used because the Trojan will open ports for itself in Windows Firewall
-
3 minutes ago, Peter Randziak said:
File rename does not change the file contents, but the scanner checks the real file type, based on the contents of the file.
I passed the info provided to the research lab to check it further.
Thank you guys, PeterThanks to everyone involved in topic with help for this threat , I believe endpoints are clean now , will keep monitoring for weird things , if something happens I will report back
And also thanks to ESET and Fortinet.
-
9 minutes ago, NoAd said:
Hello,
One of my contractors send me screen that eset found a trojan on my website, i checked VT scan and it shows 0 threats.
https://denofgamers.com
JS/Agent.QNJ
Please help me found this threat if it exist.
Also you are being blocked by Fortinet
Try to download the website files to your computer , see which file ESET is sensitive to , replace it with original , or see what has been hijacked between original and modified one.
-
15 hours ago, itman said:
I find it interesting that Eset which actually discovered this attack method;
can't stop the .dll based loaders from running.
I can confirm detections of what I sent because I sent same folder to both ESET and Fortinet because that what endpoints work with.
<Regenererede.vbs> with MD5: e627f016283c17b4badc6f5b47f677d3 - <VBS/Agent.77d3!tr> <SciLexer.dll> with MD5: 688c0480ed192ed336911d7ed3730561 - <W32/Rugmi.0561!tr> <Fruit.png> with MD5: c2a09a3c72717c71a6ac22c9f342a0d2 - <Data/Agent.STGP!tr> <ms.png> with MD5: 7b2f3421621a080c2043e6c90821c618 - <Data/Agent.STGP!tr> <Fruit.png> with MD5: fd5cb5160053fcd028ad81016357dff5 - <Data/Agent.STGP!tr> <Pine.png> with MD5: 7f5546e1202e06e17c3eabe86107a504 - <Data/Agent.STGP!tr> <Fruit.png> with MD5: 0086f1ed58e6516027bdc7d8a6c2c9ad - <Data/Agent.STGP!tr>
-
So , since not most of the files are detected , most of them to be found in AppData/Roaming , with weird namings or Adobe , or in Local as Bhromium something like this , and somewhere in AppData you can find the firefox
Simply searching for vlc.exe , firefox.exe , python.exe , notepad++.exe in AppData , will show you where it is staying most likely, and you can manually remove them
Blocking *.imgur.com , and C&C server that is found on AnyRun report , will isolate the Trojan , the load cannot be downloaded from imgur again, and if there was infection , there is no connection to C&C
ESET can pick it and clean the infected Powershell , and clean the things that was reported earlier in Threat , other scanners like Hitman , didn't pick anything , ESET did all the job , but still unpicked stuff , I deleted them manually.
Task Schedulers for VLC and Python and Notepad ++ which are the legit softwares , but they are using them to load the Loads
Once all cleaned , and schedulers disabled and removed , it shouldn't come back to life , nor be alive.
1 hour ago, itman said:In regards to the .vbs script that only Symantec detects, the VT behavior analysis note a YARA detection rule. That rule shows code which appears to scan for presence of AVG being installed. Since Avast appears to detect above linked steganography malware, those .png files might contain malware.
Thanks for the note bro
Actually this photo from BleepingComputer post you mentioned
.png)
is actually how the trojan works
File(came through whatever way) --> dll with whatever vulnerable software --> PNG from IMGUR -->Powershell to C&C (communication blocked by Fortinet first) , then ESET was installed to clean Powershell , which was successful to do so.
Since dll beside a trusted application is a stealthy way for a malware to proceed , since everything mark is Trusted/Safe then trojan have no problem to proceed however it likes
With pngs being downloaded from a Trusted/Safe place , no webfilter/dns filter would stop imgur.com unless it was filtered on purpose to stop users from accessing it
Powershell would silently communicate with it's c2c server without being detected by anyone unless the c2c and the shell are detected by security vendors.
If shell is not detected, and will be always revived by Schedulers if something happened to it , then access would be granted to the device all the time , and then anything can happen , ransomware or any other attacks.
-
10 minutes ago, itman said:
Ahh, the old file renaming after download on the target device trick.
Of note is Eset doesn't consider a file rename to be a file modification which would result in a re-scan.
Most scanners doesn't care about images in their nature I think? , this is why now malware developers use this way
And since uploading the image to a very well known place like imgur, when the Trojan communicates with imgur , you will find it normal , someone is surfing photos.
And the trojan would evade any web/dns filters you would set , since Imgur is trusted.
Quote<Fruit.png> with MD5: 0086f1ed58e6516027bdc7d8a6c2c9ad - <Data/Agent.c9ad!tr>
This is one of the Fruits.
-
4 minutes ago, itman said:
These appear to be benign .png files. That is unless stenography is being deployed: https://www.bleepingcomputer.com/news/security/worok-hackers-hide-new-malware-in-pngs-using-steganography/
In regards to the .vbs script that only Symantec detects, the VT behavior analysis note a YARA detection rule. That rule shows code which appears to scan for presence of AVG being installed. Since Avast appears to detect above linked stenography malware, those .png files might contain malware.
Those are the threats my brother , the trojan downloads them from imgur , to stay stealthy , and then will be changed to the wanted extention , fortinet already detects one of them , Fruit.png
With every fake program the Trojan uses , it will have a .png file for it
Notepad++ , VLC , Python , Firefox
They are all legit versions , but probably some kind of old versions that have vulnerabilities , and Trojan uses them to acheive what need to be achieved , and communicates to C&C with Powershell , but ESET can stop it and remove it (powershell one).
-
I have sent more archieves that are supposed to be threats , they all have same password of "infected"
they are attached on my email also with ESET sending.
example of files :
-
5 hours ago, Ond said:
Also one more small thing i also noticed before was that the malware or whatever type of that was downloading the infected files again and again using PowerShell.
Try using this to prevent the script from running till you find the source of it :
https://www.thewindowsclub.com/how-to-turn-on-or-off-windows-powershell-script-execution
Look in System Scheduler , and look in Startup entries , this is the most usual places of how a malware could keep reviving itself after being removed.
-
2 hours ago, itman said:
Bottom line - we are looking at an ATP level attack here.
I think so also






ESET Endpoint Antivirus for Linux 10 BETA
in ESET Endpoint Antivirus for Linux 10 BETA
Posted · Edited by Nightowl
I would just use my current one, I will just upgrade ESET in my computer as v9 is already installed.
Thank you