-
Posts
12,334 -
Joined
-
Last visited
-
Days Won
326
Posts posted by itman
-
-
-
4 hours ago, tman555 said:
Can opening the port through Windows Firewall work?
Assuming ESSP Firewall Filtering mode is set to Automatic which is the default setting, the Win firewall is not your issue.
-
48 minutes ago, tman555 said:
This is what appears when I click on the notification of proxy gui
The first alert states "The license will expire soon." Is this a trial license?
The second alert states "Operating system updates available."
As far as the limited cloud access warning goes;
QuoteResolve the "Limited Direct Cloud connectivity" warning
TCP/UDP port 53535 must be open
Communication with ESET's servers has changed and communication on UDP and TCP port 53535 must be allowed on a firewall for ESET LiveGrid, Antispam and Web Control to work. To resolve an ESET product with a limited Direct Cloud connectivity issue, TCP/UDP port 53535 must be open.
You may be unable to access an ESET Cloud connection due to a temporarily disabled internet connection or a network outage from your service provider.We recommend checking the internet connection with your internet service provider or using a different network and changing the Domain Name System (DNS) to, for example, 8.8.8.8.
If the issue remains, we recommend you check the connectivity to all ESET LiveGrid, Web control/Parental Control and Antispam IP addresses on the given ports.
-
What is the second Eset notification for?
I suspect one or more of your Eset protection mechanisms are disabled. Open the Eset GUI and verify no alerts are shown.
-
FYI;
QuoteVarious tools can be used in order to hijack a certificate from a trusted binary and use it to a non-legitimate binary.
python sigthief.py -i consent.exe -t mimikatz.exe -o signed-mimikatz.exe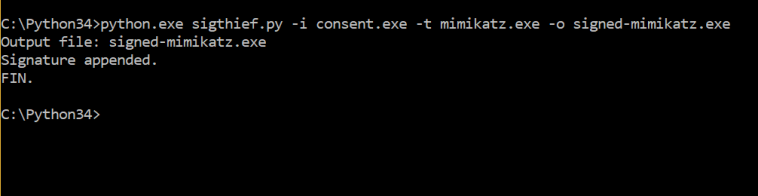 Sigthief – Stealing Certificates
Sigthief – Stealing Certificates
SigPirate.exe -s consent.exe -d mimikatz.exe -o katz.exe -a SigPirate – Stealing Certiificates
SigPirate – Stealing Certiificates
The consent file is an executable which is part of Windows operating system and therefore it is digitally signed by Microsoft. The binary will appear to have a digital signature of Microsoft.
 Malicious Binary with Trusted Certificate
Malicious Binary with Trusted Certificate
As previously the digital signature will fail to validate.
https://pentestlab.blog/2017/11/06/hijacking-digital-signatures/
-
2 minutes ago, sovchen said:
Except it's not a problem. That post is an example of the functionality I need. A wildcard rule would be exactly what I don't want in this case.
I was referring to the multiple Deny rules you created. The Allow rule would be positioned above the wildcard Deny rule so that it would execute first.
-
1 hour ago, sovchen said:
Note how I have multiple python installs working out of different locations in my filesystem. The firewall rule specifically points to the path of the executable.
This has always been a problem with Eset firewall rules. It would be solved by allowing wildcard "*" specification in path specification as the HIPS currently does;
e.g. W:\*\Python3.10.6\python.exe.
-
One possibility is this hack method: https://attack.mitre.org/techniques/T1036/001/ .
You will need to closely examine the signatures of the files that are generating these Eset detections.
-
My own opinion here is Eset should commission SE Labs to perform ransomware testing as CloudStrike did: https://selabs.uk/reports/enterprise-advanced-security-ransomware-crowdstrike-2022-oct/ .
-
2 hours ago, Purpleroses said:
I also see it under Nvidia web helper .exe and nvcontainer.exe
Nvidia web helper is GeForce Experience which I purposely never allow to be installed whenever I update my nVidia graphics card drivers.
I have never seen 127.0.0.1 used in conjunction with nvcontainer.exe. Suspect that has something to do with GeForce Experience running.
-
31 minutes ago, Purpleroses said:
I noticed under network connections this address 127.0.0.1 listening under some of my connections
If its ekrn.exe where the 127.0.0.1 connection shows, it is normal activity. Eset firewall proxy's network traffic using localhost. Also svchost.exe - IP Helper service uses 127.0.0.1. Finally, Firefox also uses 127.0.0.1 to proxy network traffic.
-
Based on this posting;
QuoteHi! I have a firewall that scans HTTPS traffic, and Proton Mail Bridge does not accept the certificate. (Which makes sense.) I would like to allow the traffic to skip inspection. What domains or IP addresses are accessed by the Bridge that can be excluded?
https://www.reddit.com/r/ProtonMail/comments/xsaspx/what_domainsip_addresses_used_by_proton_mail/
The issue is Eset SSL/TLS protocol scanning. Exclude the .exe associated with the Proton Mail Bridge app from SSL/TLS protocol scanning and see if that resolves the issue.
-
Also as I suspected, CVE-2023-4863 affects Microsoft software including Windows itself;
QuoteReports indicated that the vulnerabilities (CVE-2023-4863, CVE-2023-36761 and CVE-2023-36802) in Microsoft Windows and Server, Microsoft Edge, as well as Microsoft Office, Word and 365 Apps are being exploited in the wild
https://www.govcert.gov.hk/en/alerts_detail.php?id=1107
It is therefore imperative that Windows Sept. Cumulative update plus Office and 365 app updates be performed immediately.
-
Add Opera to the list of affected browsers;
QuoteFortified Security with Chromium 116.0.5845.188 (CHR-9416): The cornerstone of Opera 102’s security enhancements is the integration of Chromium version 116.0.5845.188. This update addresses crucial security issues, including CVE-2023-4863, to ensure your browsing sessions are safer than ever. Staying current with Chromium is fundamental for security in today’s digital landscape.
https://blogs.opera.com/desktop/2023/09/opera-102-0-4880-51-stable-update/
-
Also, this vulnerability just doesn't affect web browsers;
QuoteThe heap buffer overflow (CVE-2023-4863) vulnerability in the WebP Codec is being actively exploited in the wild.
A significant vulnerability in the WebP Codec has been unearthed, prompting major browser vendors, including Google and Mozilla, to expedite the release of updates to address the issue.
-
Update (9/13/2023): So far the Web Browsers that have confirmed a fix and released an update include: Google Chrome[1], Mozilla Firefox[2], Brave[3], Microsoft Edge[4], and Tor Browser[5]. If your browser of choice is using Chromium then expect an update to already be rolled out or will be done shortly.
-
 Important: Let me make it perfectly clear that this vulnerability doesn't just affect web browsers, it affects any software that uses the libwebp library. This includes Electron-based applications, for example - Signal. Electron patched the vulnerability yesterday. Also, software like Honeyview (from Bandisoft) released an update to fix the issue. CVE-2023-4863 was falsely marked as Chrome-only by Mitre and other organizations that track CVE's and 100% of media reported this issue as "Chrome only", when it's not.
Important: Let me make it perfectly clear that this vulnerability doesn't just affect web browsers, it affects any software that uses the libwebp library. This includes Electron-based applications, for example - Signal. Electron patched the vulnerability yesterday. Also, software like Honeyview (from Bandisoft) released an update to fix the issue. CVE-2023-4863 was falsely marked as Chrome-only by Mitre and other organizations that track CVE's and 100% of media reported this issue as "Chrome only", when it's not.
-
 Who uses libwebp? There are a lot of applications that use libwebp to render WebP images, I already mentioned a few of them, but some of the others that I know include: Affinity (the design software), Gimp, Inkscape, LibreOffice, Telegram, Thunderbird (now patched), ffmpeg, and many, many Android applications as well as cross-platform apps built with Flutter.
Who uses libwebp? There are a lot of applications that use libwebp to render WebP images, I already mentioned a few of them, but some of the others that I know include: Affinity (the design software), Gimp, Inkscape, LibreOffice, Telegram, Thunderbird (now patched), ffmpeg, and many, many Android applications as well as cross-platform apps built with Flutter.
- Update (9/14/2023): 1Password for Mac have released an update to address the issue. 1Password (like many others) is an application built with Electron, and until all these apps upgrade to the latest version - they are considered vulnerable based on the severity of the bug.
- Update (9/15/2023): Okay, so, I thought I would give an update as I have been getting a lot of emails about this, and I can't spend so much time trying to answer each one individually. I know that Telegram Desktop made an update and I have seen Ubuntu, Debian, SUSE and other Linux platforms also actively updating their libwebp versions. I also know that software like Obsidian is going to bump their Electron version
https://stackdiary.com/critical-vulnerability-in-webp-codec-cve-2023-4863/
-
Update (9/13/2023): So far the Web Browsers that have confirmed a fix and released an update include: Google Chrome[1], Mozilla Firefox[2], Brave[3], Microsoft Edge[4], and Tor Browser[5]. If your browser of choice is using Chromium then expect an update to already be rolled out or will be done shortly.
-
On 9/14/2023 at 3:38 PM, czesetfan said:
One more addition.
I can't use wildcards ?,# in the rules?
You can use either "*" or "?" special characters: https://help.eset.com/essp/16.2/en-US/idh_config_epfw_scan_http_address_list.html .
On 9/15/2023 at 5:26 AM, czesetfan said:For example: test01.com, test02.com
test??.com should do the trick.
-
On 9/14/2023 at 7:48 PM, tommy456 said:
I Assume ESET is aware of this assumed threat,? And probably will protect the end user against it ? Just seeking confirmation
Bad assumption. Update your Chrome/Edge or Firefox browser to latest version which will apply the needed security patch.
-
On 9/15/2023 at 12:19 AM, tman555 said:
Is this an attack?
No.
By default, the Eset firewall will block inbound UPnP; i.e. protcol UDP port 1900, on the network connection default Public profile.
I assume IP address 192.168.1.1 is your router. Some routers enable UPnP traffic for connectivity checking purposes. It is also a potential security risk.
You have two choices;
1. Disable UPnP via its Router GUI setting.
2. Unblock the UPnP traffic via Eset Network Wizard which will create a firewall rule to allow the network traffic.
-EDIT- Prior to allowing this UPnP traffic through the Eset firewall, it is imperative you verify the router performs UPnP. If it doesn't, assume the router has been hacked and do not allow this traffic through the Eset firewall.
-
I would say at this point that your router/gateway is screwed up. It is either malfunctioning or has been hacked. Perform a hard reset of the router/gateway and hopefully, that will straighten things out.
-
I believe I know what happened but don't know why it occurred.
It appears you, your ISP, or whomever configured you local network has set the default gateway IP address on your local network to fe80::1 which is unusual;
QuoteOne method to make things easier is to manually assign the link-local address to the upstream router’s interfaces. If you assign the link-local address FE80::1 on each of its interfaces and if that link-local address is unique on each of those LAN segments, then this becomes the default gateway for the hosts on those LANs.
https://blogs.infoblox.com/ipv6-coe/fe80-1-is-a-perfectly-valid-ipv6-default-gateway-address/
Additionally, fe80::1 works for IPv4 gateway assignment;
QuoteWhat's neat is that it's also a perfectly valid IPv4 gateway address now. (Because, as the post mentions, it's only used to discover the MAC address.)
ip route add 0.0.0.0/0 via inet6 fe80::1 dev eth0
https://www.reddit.com/r/ipv6/comments/ne7w8c/fe801_is_a_perfectly_valid_ipv6_default_gateway/
Something happened on your PC local network that caused the default gateway address to be set to 127.0.0.1 which is the IPv4 localhost default address which caused Eset to go bonkers.
One possibility this is occurring is when Eset firewall processing set up your network connection, it had trouble identifying your network parameters such as assigned router IPv4/IPv6 gateway addresses and defaulted to using network adapter MAC address. This would explain the fe80::1 usage.
-
15 hours ago, AnthonyQ said:
IMO, as a professional and well-known testing organization, AV-Comparative won’t take PUA as Malware.
Correct I mis-posted;
QuoteWe test all consumer products with their default settings, since surveys reveal that most home users keep their security programs at advised (default) settings. There is one exception to this rule, namely that we enable detection of potentially unwanted applications (PUA) if available. However, we do not test for PUAs, and use our own checks and analysis of samples to ensure that no verified PUA samples are counted in our test scores.
https://www.av-comparatives.org/faq/
A long discussion of this topic in this thread: https://forum.eset.com/topic/12569-question-about-avc-real-world-test/
I do know AV-C tests always contain a few samples Eset misses. Also, Eset results are better on other AV lab tests:
https://selabs.uk/reports/endpoint-security-eps-small-business-2023-q2/
https://www.mrg-effitas.com/wp-content/uploads/2023/08/MRG_Effitas_360_Q2_2023.pdf
https://avlab.pl/en/recent-results/
Bottom line - you can't fully evaluate an AV product effectiveness based on one AV lab test.
-
I also checked a few web sites using GZip in Firefox that Eset is perform SSL/TLS protocol scanning. They all show the Content-Encoding: gzip header.
The mystery is why Content-Encoding-Over-Network: gzip header is being used on your web based app.
-
Also, open a command prompt window.
1. Enter this command, nslookup journal.stikosa-aws.ac.id
Take a screen shot of the output.
2. Enter this command, nslookup google.com
Take a screen shot of the output.
Post both screen shots.
-
As far as this:
Quoteredirect=www.msftconnecttest.com/redirect
goes: https://www.pcwdld.com/fix-msftconnecttest-redirect-error





Interactive firewall mode poll
in ESET Internet Security & ESET Smart Security Premium
Posted · Edited by itman
I question the wisdom of the Trusted Publisher option. Certificates can be spoofed. Unless Eset is actually verifying the process is validly signed; note this could be for every process run with the same Pulisher in the case of Trusted Publisher only evaluation criteria, the option should be eliminated.